
CASB is a word that keeps popping up every time there is a discussion about cloud security. But what exactly is a CASB? How does it work?
Read More
Keys to the Digital Transformation Credentials work as the keys to digital transformation. If organizations are still in two minds about implementing employee credential security. Verizon-2015-Data-Breach-Incident-Report needs
Read More
While the frequency of cyber attacks is increasing day by day and the ferocity of these attacks has been growing with each passing day, so is the
Read More
Introduction to Cloud Computing Cloud computing is a term you get to hear everywhere, and if you are in a business, you might be wondering if you
Read More
Need for Identity and Access Management The days of choosing ‘ABC’ as the password letters are long gone. Nowadays even the combination passwords are also passé. Capital
Read More
SaaS Security Data Breach The onus of sensitive data protection is a shared responsibility of the enterprise and the cloud service provider. Of course, the service providers have
Read More
Reaching Compliance With CASB Cloud offers a wide range of benefits like mobility, scalability, flexibility, and convenience. Hence, enterprises must migrate to cloud platforms to increase their productivities.
Read More
Cloud Visibility and Security as Obstacles in the way of Cloud Adoption Organizations for sure want to migrate to cloud services, for it offers a plethora of
Read More
Zero Trust is an organization security model in light of an exacting character confirmation measure. The structure directs that alone validated and approved clients and gadgets can
Read More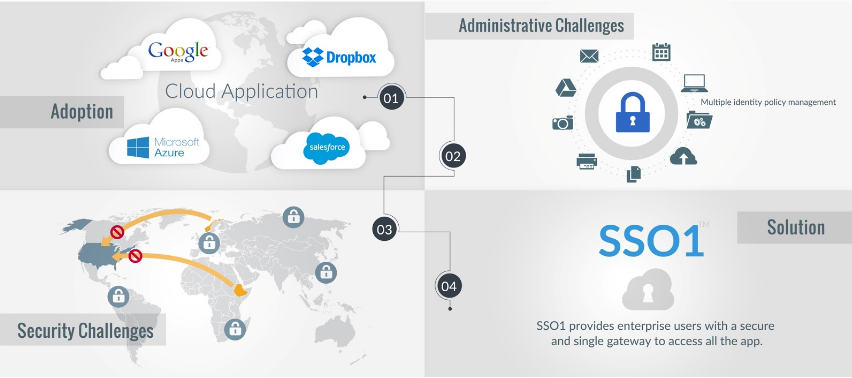
Cloud adoption has been on rising for the last 8-9 years. For all good reasons, enterprise finds cloud-based applications to be cost-effective and bring efficiency in their
Read More