Cloud adoption has been on rising for the last 8-9 years. For all good reasons, enterprise finds cloud-based applications to be cost-effective and bring efficiency in their overall process. However, there is no single universal cloud application that will work for every need of an enterprise. Based on the functional objective of the enterprise, various cloud applications are adopted such as Zoho, SalesForce for CRM, Google for Work/Office365 for messaging, Marketo for marketing, and so on. Each of the cloud-based applications hosts web applications and serves customers across the world in a multi-tenant manner.
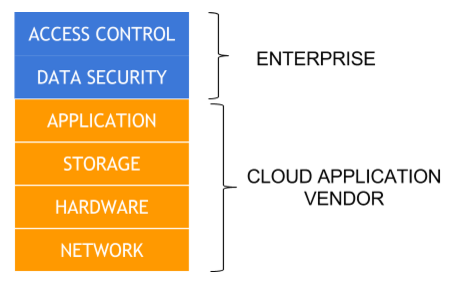 |
The cloud application provider’s responsibilities are to ensure the physical infrastructure on which the application is hosted. The CSP ensures the solution is scalable, robust, and secure. The data within the cloud belongs to the customer and it is the responsibility of the customer to ensure the data is secure and safe.
There are Two Set of Problems with Cloud-Based Applications
- Managing Identities across multiple applications
- Managing Security across multiple application
Problem 1: This problem relates to managing identities across multiple applications in a unified manner. Provisioning and de-provisioning of users across cloud applications is a huge challenge. The problem is however resolved through Single Sign-On or Identity Access Management solutions. Many vendors are in this area providing very robust and rich solutions.
Problem 2: This problem relates to managing security across all the adopted cloud applications by the enterprise. Some of these security controls are provided by some of the cloud applications but managing across multiple applications may become a challenge. Some analysts referred to this area of concern as Cloud Access Security Broker(CASB) or Cloud Security Gateway(CSG). There is a good number of vendors in this area. But all of them use API methodology to determine risk or security concerns within a cloud application. CloudCodes uses a different approach.
CloudCodes uses a preventive approach to secure multiple cloud applications through CloudCodes for Business (CFB). It provides controls to the IT team to prevent unauthorized access to the enterprise web-based applications. It has taken a reverse route to cloud-based single sign-on or identity access management i.e. it is providing SSO/IAM as part of its cloud security offering. It adds a cloud-based firewall on top of all cloud applications to ensure authorized users access the application in a secured manner. It is also adding other capabilities of CASB such as using API based approach to determine any security-related risks for cloud applications.
The objective is to add capabilities to the product CloudCodes for Business (CFB) to enhance the level of cloud security for organizations’ cloud-based applications.

