What is the Future of Cyber Security?
The quantity of IT frameworks, cloud benefits, and associated gadgets is continually expanding. All of these frameworks and devices create vast volumes of data, and this data must be ensured throughout.
Our device Security barriers are now totally mechanized. Our working frameworks are safely arranged, from firmware startup to the practical framework that runs applications in secure equipment implemented reasonable limits, than in recent memory. Whenever left alone in their default express, our working frameworks will auto-update themselves to limit any known vulnerabilities that have been tended to by the OS seller.
Our lives are supervised in the online space. Innovation influences all parts of present-day life. The vast majority of our necessary frameworks are interconnected and driven by devices. Later on, we can anticipate that more choices should be robotized. Companies with device frameworks will be significantly more established.
The need for cyber security in this time and age can never be overemphasized. Organizations across businesses are presently putting resources into cybersecurity experts to guard their information.
Few Industrial Predictions:
- More Vulnerabilities: Cybersecurity dangers are probably going to turn out to be progressively extreme, because of the rise of interconnected gadgets. More mortgage owners are introducing IoT (Internet of Things) devices in their homes. Offices are gradually receiving savvy innovation in their training. Indeed, even automated vehicles are nearly entering the world's standard vehicle division.
With innovation driving the more significant part of our own and business commitment, life has gotten simpler. Access to data is currently consistent, and the world is presently more practical than any other time in recent memory. Be that as it may, there is a dangerous chance most definitely. - Better Detection: Interruption identification is an essential ability concerning finding and relieving the impacts of harmful digital action. In any case, as important as it seems to be, very few cybersecurity engineers have these aptitudes. Also, numerous associations are yet to find their pertinence in information Security. However, all signs are pointing towards the chance of this innovation getting progressively far, reaching in the coming years.
- Efficient Developers: Information offenders forcefully invade databases in many organizations' product codes. Most web-based business sites have disordered in-house programming development teams who care less about secure software advancement. To numerous business people today, stable programming advancement is an unnecessary cost. It will change individuals to keep on finding the incredible information potential that protected programming has.
- Increased AI: Organizations will have the option to depend on keen devices to deal with the majority of occasion observing and occurrence reaction. The up and coming age of firewalls will have AI innovation incorporated with them, permitting the product to perceive designs in web demands and naturally obstruct those that could be a danger.
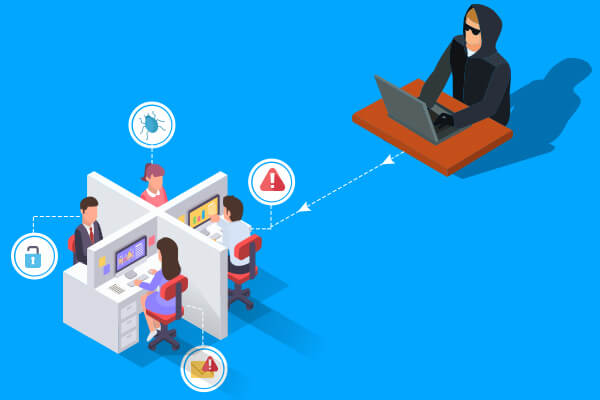
Specialists additionally expect the common language capacities of AI to assume a significant job later on for cybersecurity devices. The hypothesis is that by filtering enormous bits of information over the web, AI frameworks can figure out how cyberattacks begin and propose answers for chiefs inside the association. - Cyber Threats: Most information criminals are harmful individuals attempting to tarnish the reputation of an organization. We are probably going to see the rise of monetarily stimulated digital fraudsters who will try to adapt digital attacks. These aggressors will use new specialized abilities and sophisticated assault techniques to find ill-equipped in-house IT groups. Sadly, digital aggressors could be the eventual fate of common fear-based on oppression.
Support the management is additionally a vital bit of any company's cybersecurity methodology. Organizations should anticipate crises by building up a disaster recuperation plan. By running usual reinforcements on all center frameworks, you can recover from a blackout or information penetrate in a sensible measure of time.
In any case, with regards to modern cybersecurity, maybe no device is more significant than preparing. The best organizations run meetings all the time for new and existing workers to teach them about what dangers exist on the web and how to secure themselves and the organization.
There have been upgrades in password word administrator programming. The vast majority of which plan to rearrange and strengthen online security by expelling a large segment of the manual attempt from the undertaking through calculations that propose and store passwords sufficiently complex to diminish your odds of being hacked.