IP Restriction For Cloud Security
Gain Granular Control On Your Enterprise Data Accessibility With IP Restriction
IP Restriction is one of the most popular, most demanded, and most needed feature by many organizations across various industry verticals under their Cloud Security strategy. Of all our customers, xy% have opted for IP restriction and have agreed that IP Restriction, along with other Access Control features, has indeed played a vital role in securing their cloud app infrastructure. But before we get into further details, let us dig up the basics.
What is an IP address? What is IP Restriction?
Many of the internet users still don’t know what an IP, Internet Protocol, means. An IP address is like a digital address for your computer for the internet to know where to reach you. In a nutshell, it is a network address that allows one computer to communicate with another over the Internet. Every website has its IP address.
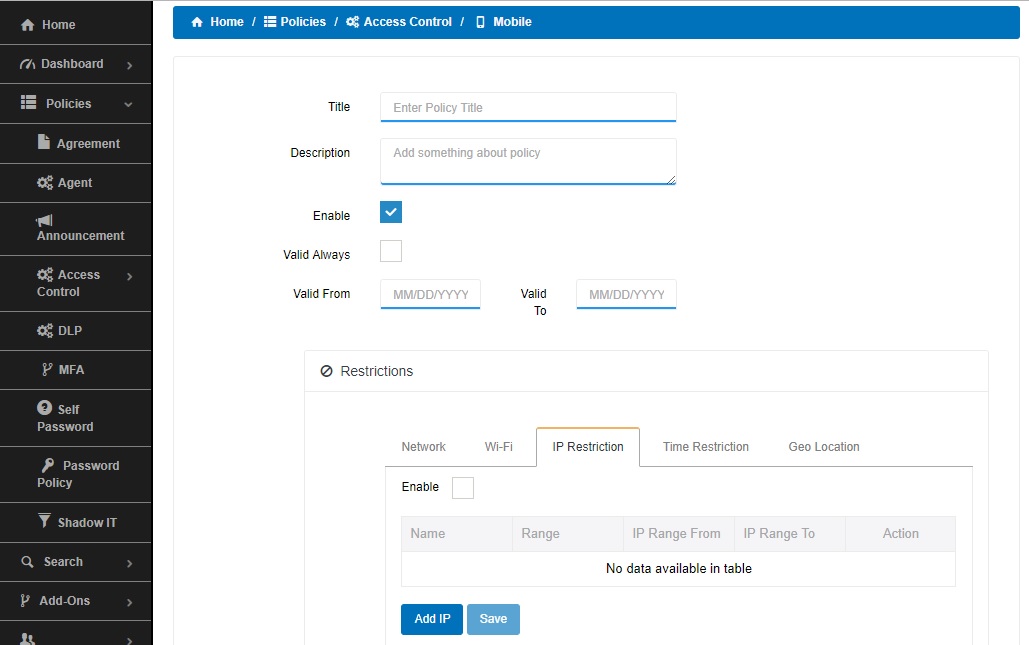
IP restriction feature of CloudCodes For Business enables the IT admins to restrict access of their corporate data from specified, pre-defined IP addresses only. An IT admin can Whitelist or Blacklist IP addresses for the entire organization, specific OUs, or a single user from the admin dashboard of CloudCodes For Business.
Why Is IP Restriction Important For You?
Cloud computing has enabled users to access business data from anywhere, any time, and any device. It has also become a bane in a few scenarios when it comes to data security. Cloud computing’s flexibility has come to reduce the visibility of the IT team in the user activities, due to which the IT admin may not able to track the origin and reason of a data loss on time.
With our IP Restriction policy in action, any user trying to access their cloud apps from an unknown IP address will be restricted to access corporate data even if he provides correct credentials. From a security point of view, this will prevent unauthorized/potential data thief from accessing, looting, or leaking corporate data, even if he was able to punch in the right credentials.